For VCSA appliance, if a customer CA-signed certificate is required, there are two ways to generate the CSR and replace the certificate:
- VMware Certificate Manager in command; and
- Certificate Management in vSphere Client
The 1st option is commonly used and described as in below VMware KB article:
https://kb.vmware.com/s/article/2112277
This post is to illustrate the second way by using vSphere Client.
Below steps are demonstrated in vCenter Appliance version 6.7 with integrated PSC by replacing the machine SSL certificate.
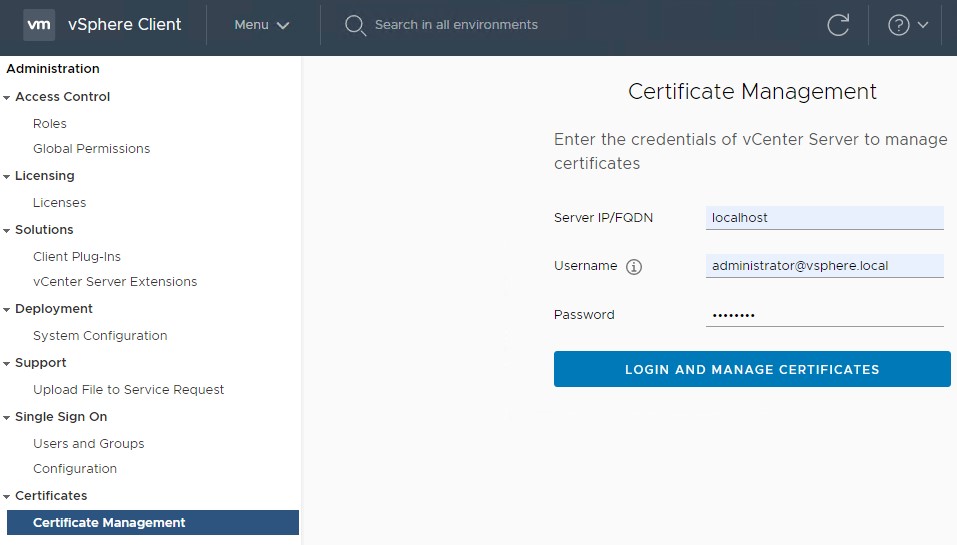
Step 1: Login vSphere Client via administrator@vsphere.local. Navigate to Administration -> Certificates -> Certificate Management. Login with administrato@vsphere.local to localhost or the vCenter you would like to manage.
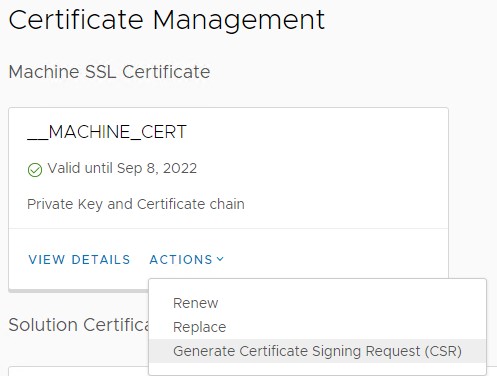
Step 2: To replace the VCSA Machine Cert, the first step is to generate a CSR. Click “Action” and Select “Generate Certificate Signing Request (CSR)”.
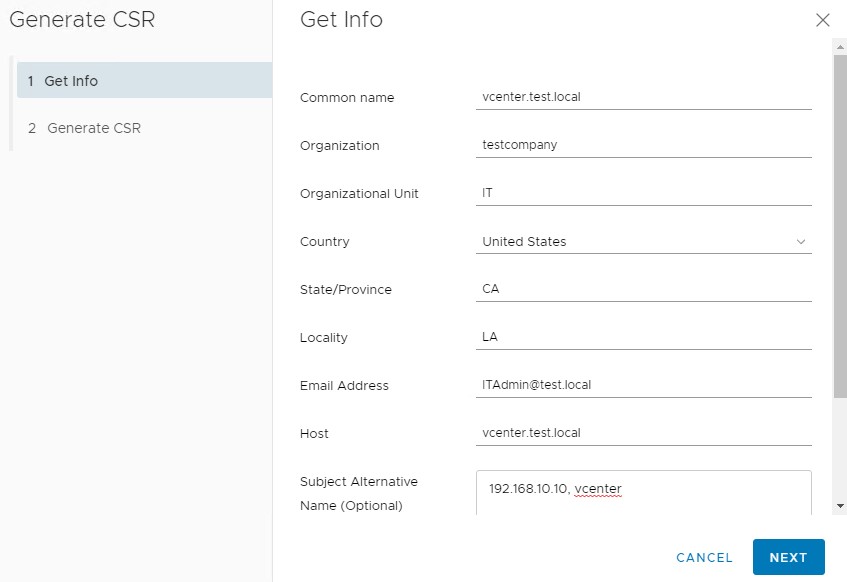
Fill the information as required. In “Subject Alternative Name” section, it is recommended to put IP address and short host name of vCenter Appliance. Click “Next” to generate your CSR.
Step 3: Send the CSR to CA admin in your organization to receive the customer certificate.
It is noted that it is required to generate the customer certificate with full chain. This is important as VCSA will import the customer root and intermedia CA certificate from the full chain.
Also, you might need to convert certificate to “.cer” format via below command if received a cert file with “.p7b” format.
openssl pkcs7 -print_certs -in certificatename.p7b -out certificatename.cer
The openssl utility can be installed on your workstation/laptop, or you can use the existing openssl utility in vCenter Appliance by upload the cert to it.
Step 4: Apply the new certificate by clicking “Action” and selecting “Replace”.
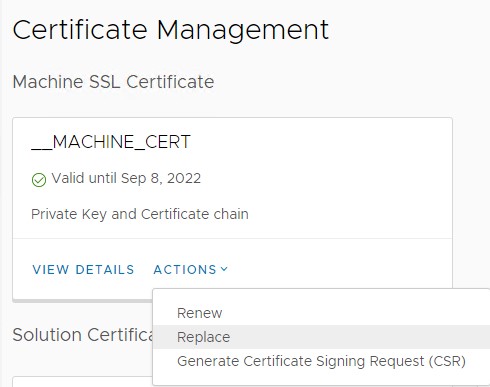
In the pop-up windows, there are two files need to be uploaded. The new certificate file and private key.
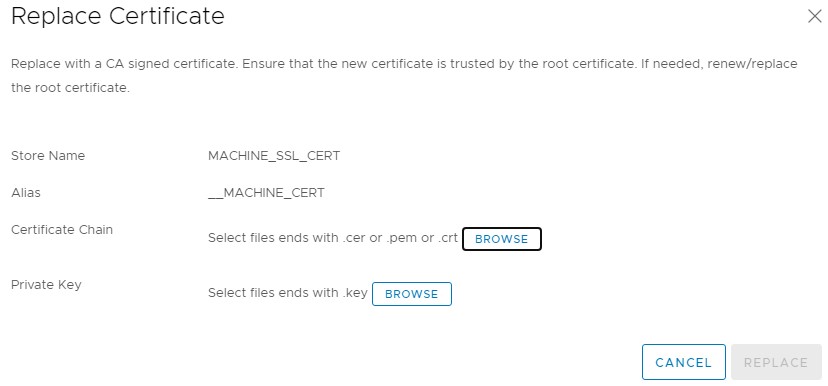
As in VCSA 6.7, the private key is not shown and downloaded in CSR step. Therefore, to obtain the private key, it can be queried via below command in vCenter Appliance.
/usr/lib/vmware-vmafd/bin/vecs-cli entry getkey --store MACHINE_SSL_CERT --alias __MACHINE_CSR
Step 5: After replacing the customer cert, restart the vCenter service with below commands to apply the new certificate.
service-control --stop –all service-control --start –all
For now, the machine certificate should be replaced with a customer signed certificate.
It is noted that it is always highly recommended to take a backup of your vCenter before applying the new certificate.

Thanks for the help !